Top 10 Cybersecurity Myths Businesses Still Believe
Cybersecurity Myths vs. Reality

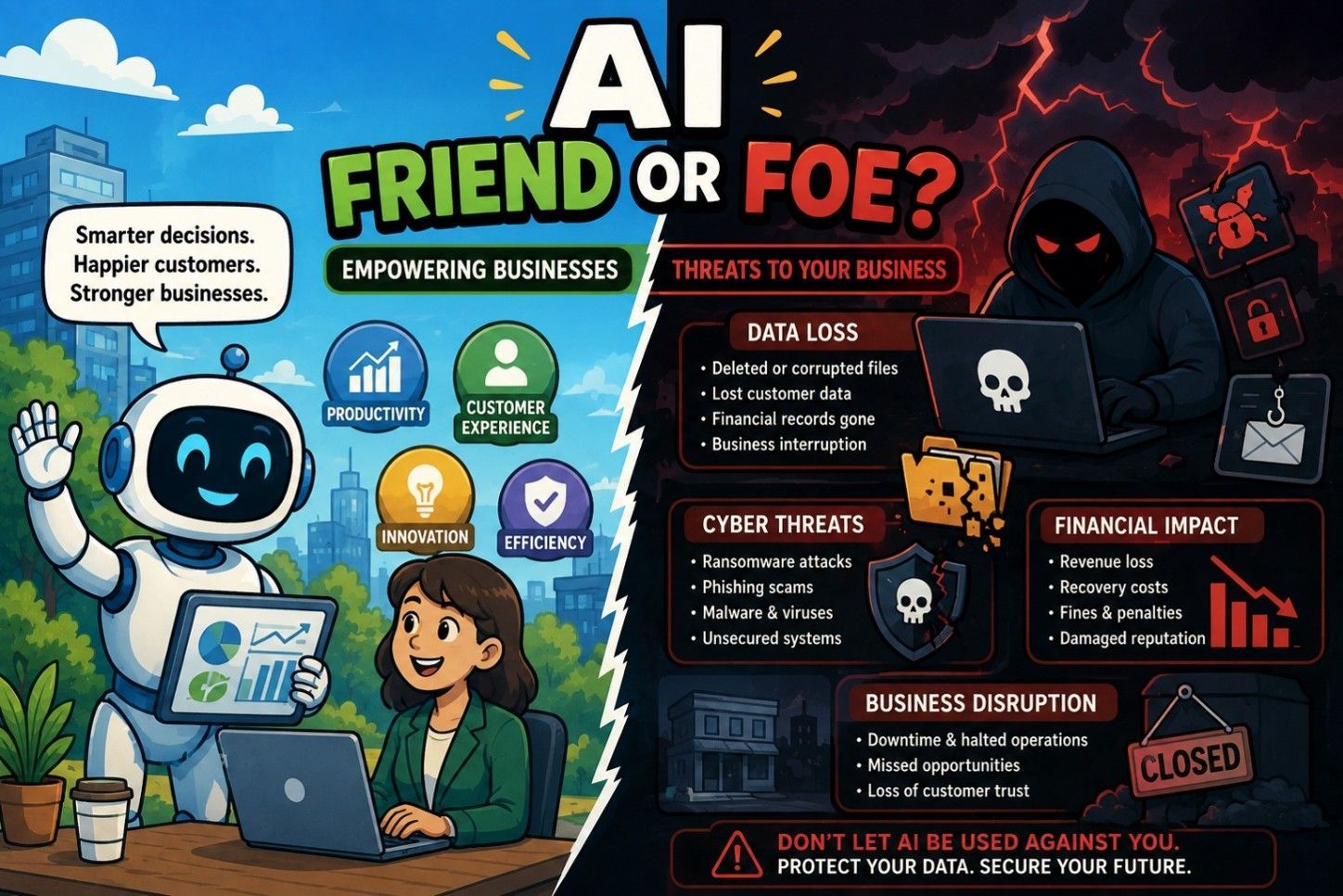
Cybersecurity myths are everywhere, and many of them influence business decisions and can create serious blind spots for business operations. When business leaders rely on these outdated beliefs, security programs stall, risk grows, and compliance becomes reactive instead of strategic.
Understanding these 10 most common cybersecurity myths isn’t just educational, it’s foundational to building a stronger, risk-based approach. So, let's clear them up.
- We’re too small to be targeted
Attackers don’t only go after large enterprises. Small and mid-sized businesses are often targeted because they’re seen as easier entry points.
- We passed an audit, so we’re secure
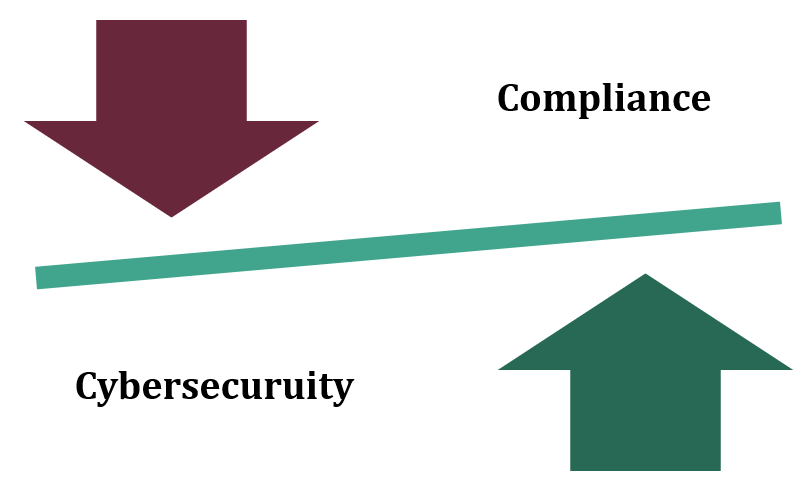
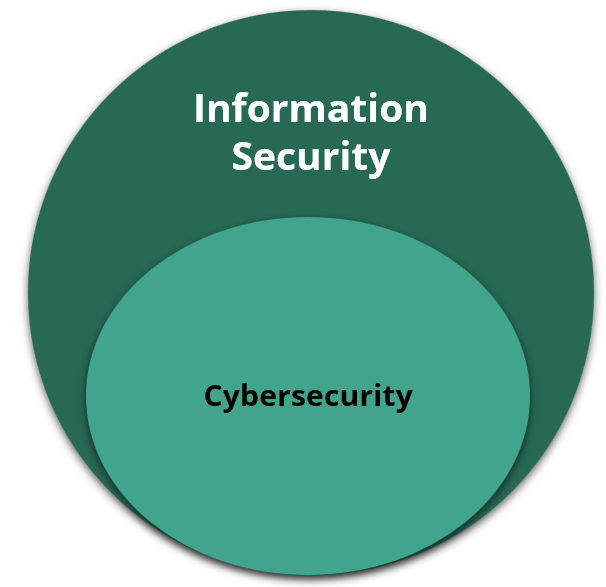
Compliance is important, but it’s not the same as security. Meeting requirements doesn’t guarantee protection from evolving threats.
- Our IT team handles cybersecurity
Cybersecurity isn’t a task. It requires leadership alignment, user awareness, and ongoing risk management across the organization.
- We have antivirus, so we’re covered
Modern attacks bypass traditional tools. A layered cybersecurity strategy and continuous monitoring are essential to reduce real risk.
- Cybersecurity is too expensive
This is a common, outdated belief about cybersecurity. Cybersecurity doesn’t have to be costly; many protective measures simply involve better use of the tools you already have, combined with well‑defined processes and informed people.
Instead of viewing security as a costly burden, it is essential we shift our focus and treat cybersecurity as a crucial investment that protects revenue.
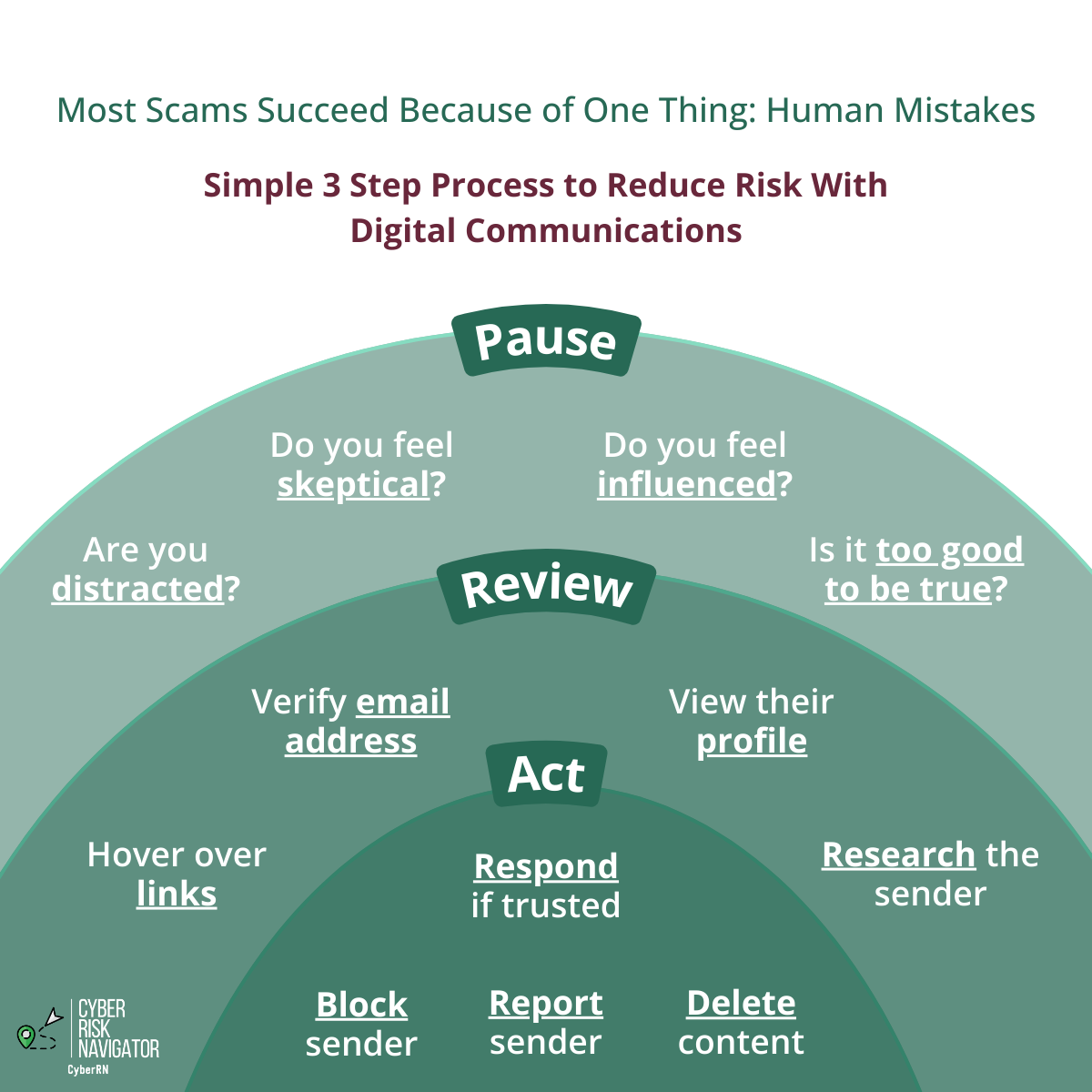
- Employees will spot phishing emails
Even trained employees can be fooled. Ongoing education and strong technical safeguards are both necessary.
- Cloud providers handle all security
Cloud platforms secure infrastructure, but organizations remain responsible for configurations, access control, and data protection.
- Cyber insurance solves the problem
Insurance helps with recovery, but it doesn’t prevent damage, reputational harm, or operational disruption.
- Security is a one-time project
Cybersecurity is not a checklist. It’s a continuous process that adapts as technology and threats evolve.
- If we haven’t been breached, we’re fine
Many organizations don’t realize they’ve been compromised until much later. Proactive risk assessments help identify gaps before incidents occur.
Moving Beyond Cybersecurity Myths With Cyber Risk Navigator
Moving beyond cybersecurity myths simply means focusing on what truly reduces risk and supports better security decisions. Cyber Risk Navigator understands that businesses are often navigating competing priorities, limited resources, and evolving threats.
That’s why these common misconceptions are worth breaking down, so leaders can make decisions based on what’s real, not what’s assumed. If you’re looking for a deeper dive into how these cybersecurity myths may be showing up in your organization, reach out to Cyber Risk Navigator. This way, you can approach security with clearer priorities and stronger direction.