Cybersecurity vs. Compliance: Difference and Why It Matters
Cybersecurity vs. Compliance
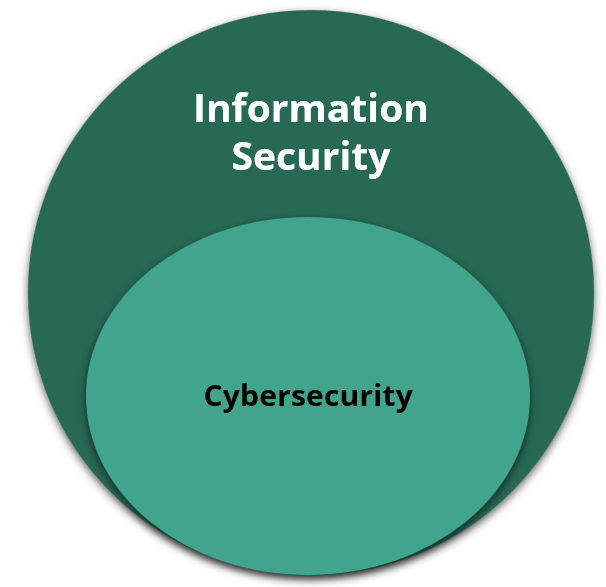
What Is Cybersecurity?
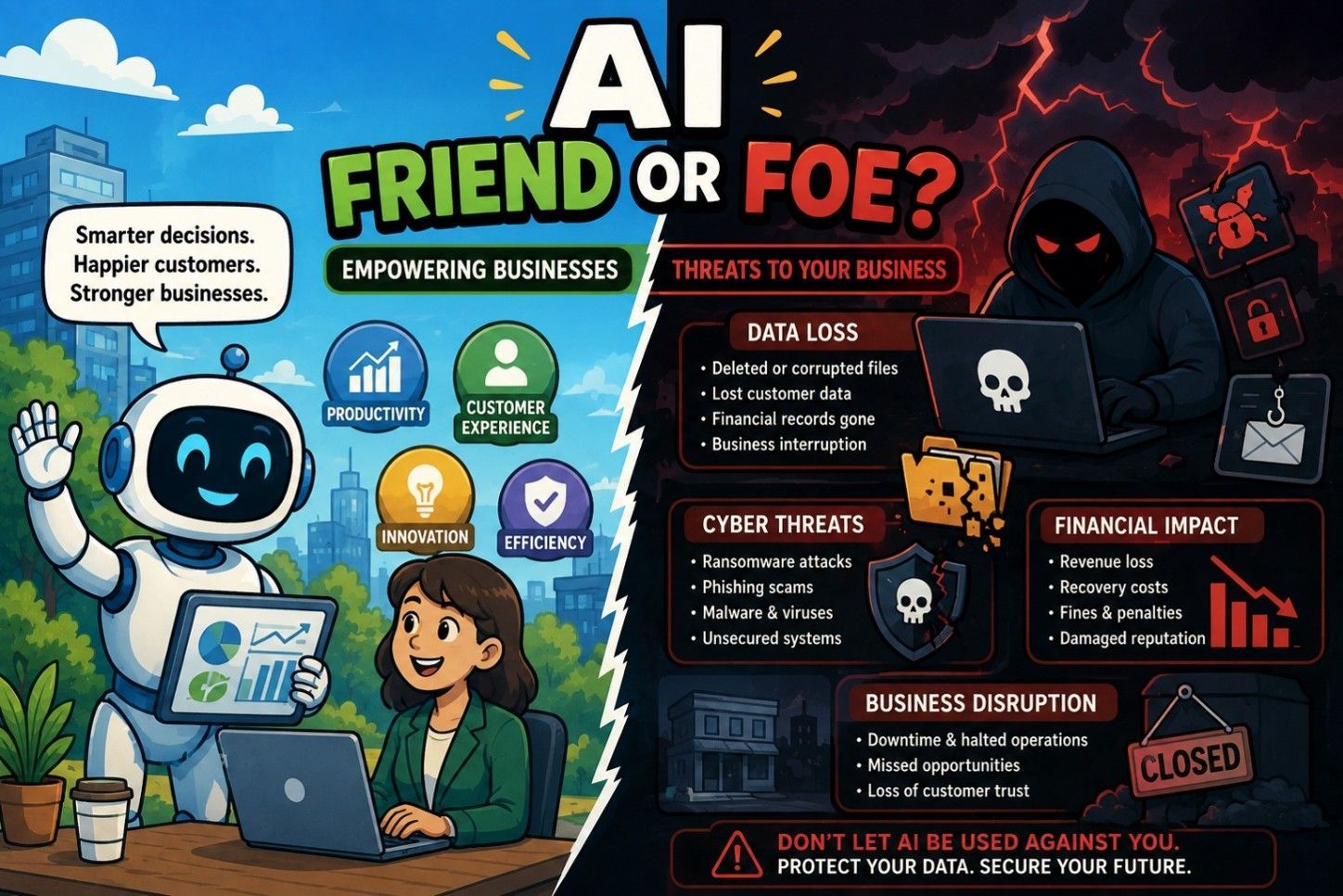
Cybersecurity is the practice of protecting your organization’s systems, data, and operations from cyber threats. That includes things like ransomware, phishing attacks, insider threats, and systems outages.
Cybersecurity is about risk reduction. It focuses on:
- Identifying vulnerabilities
- Preventing attacks where possible
- Detecting issues quickly
- Responding and recovering when something goes wrong
Cybersecurity is not a one-time project or a checkbox. Threats evolve constantly, which means security controls, processes, and training need to evolve too. A strong cybersecurity approach considers people, processes, and technology working together to protect what matters most to the business.
What Is Compliance?
Compliance refers to meeting specific regulatory, legal, or contractual requirements. These requirements often come in the form of frameworks or standards such as SOC 2, HIPAA, PCI DSS, or GDPR.
Compliance answers questions like:
- Do required policies exist?
- Are specific controls in place?
- Can you demonstrate that you follow documented procedures?
Compliance is about proving that certain expectations are met. It provides structure, accountability, and a common baseline for organizations operating in regulated environments. Compliance is important for your organization, but it is designed to define minimum requirements, not to address every possible risk.
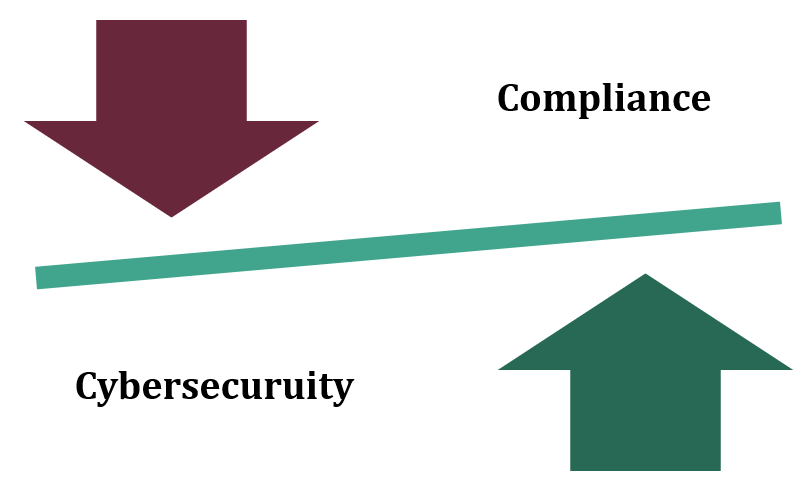
Cybersecurity vs. Compliance: What’s the Difference?
While the two are connected, their goals are different.
- Cybersecurity focuses on protecting the organization from real-world threats
- Compliance focuses on meeting defined rules and standards.
One is proactive and adaptive, the other is prescriptive and periodic. Both matter; however, they serve different purposes.
Why Compliance Alone Doesn’t Equal Security
One of the most common misconceptions is that passing an audit means an organization is secure.
Unfortunately, that’s not always the case. Compliance frameworks can’t keep up with every emerging threat.
An organization can technically meet all required controls and still have gaps that attackers exploit. This is why breaches often occur at compliant organizations. This doesn’t mean compliance has failed; it simply wasn’t designed to be a complete security strategy on its own.
Why You Need Both Cybersecurity and Compliance
When cybersecurity and compliance work together, they reinforce each other. Cybersecurity is the foundation that Compliance validates against. Together, they help organizations:
- Reduce the likelihood and impact of incidents
- Demonstrate due diligence to regulators and partners
- Build trust with customers and stakeholders
- Support long-term business resilience
It’s not about choosing one over the other; it’s about integration.
How to Align Cybersecurity and Compliance in Your Organization
A strong starting point is to focus on risk first, not just requirements. Conducting a risk assessment can help identify where compliance controls support security, and where additional safeguards are needed.
To conduct a risk assessment successfully:
● Map security controls to compliance requirements
● Ensure policies reflect real operational practices
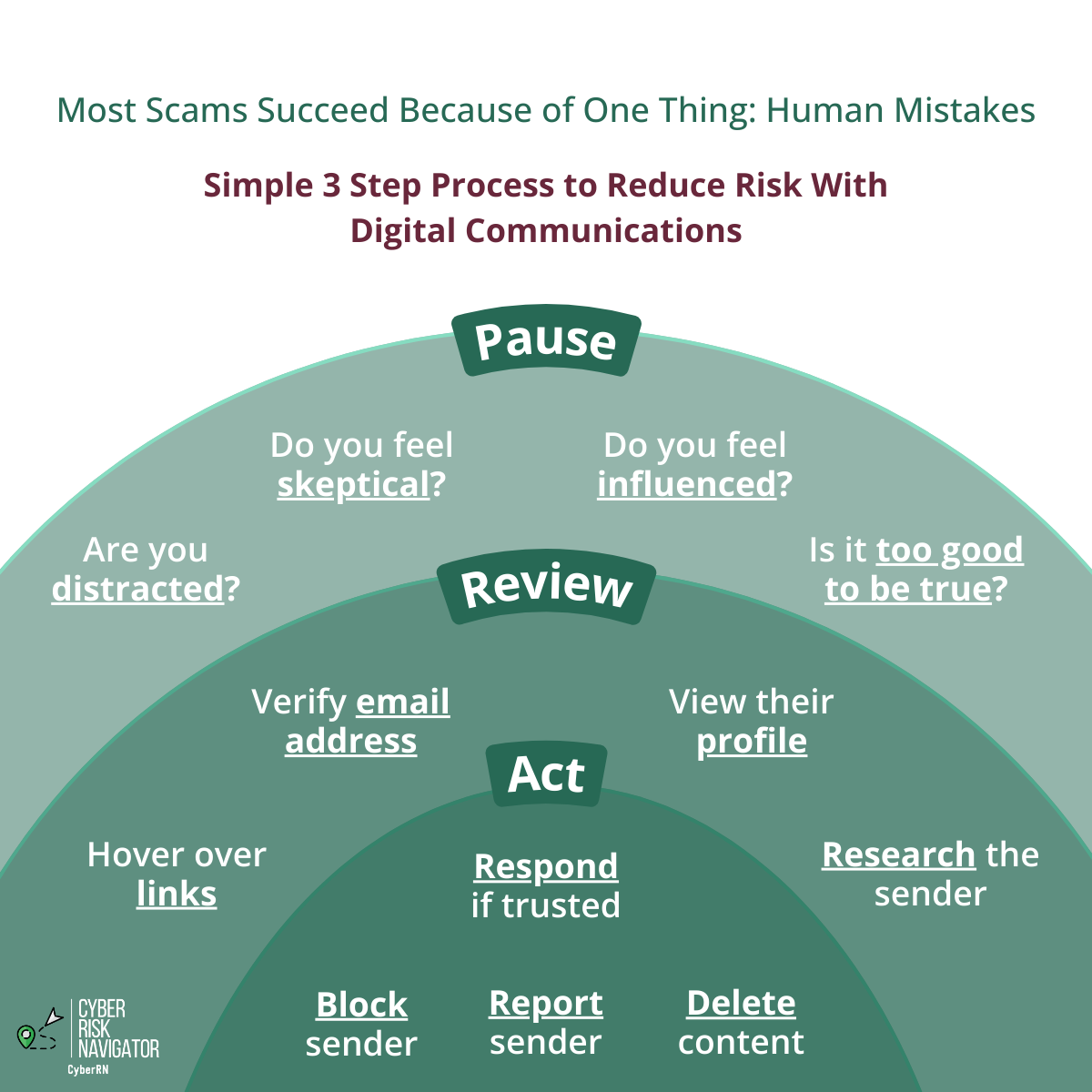
● Invest in employee awareness and training
● Revisit controls regularly as the business and threat landscape change
Having experienced cybersecurity guidance can make this process clearer and more manageable.
You Don’t Have to Navigate This Alone
Cybersecurity and compliance can feel overwhelming, especially when expectations are high and time is limited. That’s where having the right guidance makes all the difference. If your goal is to reduce risk while meeting compliance expectations, start by reaching out to Cyber Risk Navigator. This way, your organization has experienced cybersecurity leadership translating confusing compliance requirements into clear, defensible actions, so your teams know exactly what to prioritize, implement, and maintain.